Reverse SSH tunnel in 2021 easiest way
To access a Linux device terminal while it in a different network, without exposed public IP, there are a few solutions that may do the job perfectly. A reverse SSH tunnel is known as one of the easiest, secure and lightweight implementation for accessing Linux devices remotely, and here at JFrog Connect we provide a ready-to-use solution that takes less than 60 seconds to integrate for any Linux based device.
Before that, what Reverse SSH tunnel really is?
SSH tunnel is a client-server based architecture protocol for accessing Linux devices shell over IP. SSH tunnel uses a network port for creating a connection session between the server that listens on the chosen port and the client which sending an SSH request on that port. This way, The client-side access the server shell remotely.
Reverse SSH is based on 2 regular SSH sessions, one goes from the client to the server, similar to regular SSH tunnel and the second session is inside the first tunnel, while there is another server on the client-side. In other words, the second session is inside the first SSH session, while this time, the server-side behaves as the SSH client and the client-side behaves as an SSH server.

What we can do with a Reverse SSH tunnel?
Reverse SSH tunnel can help you access Linux device shell without exposure of open ports to the internet world. This way can help us securing the devices by keeping it under the radar of hackers. Another common situation is when the Linux device IP is over NAT what makes it impossible to reach the device IP over the internet.
What is JFrog Connect remote control?
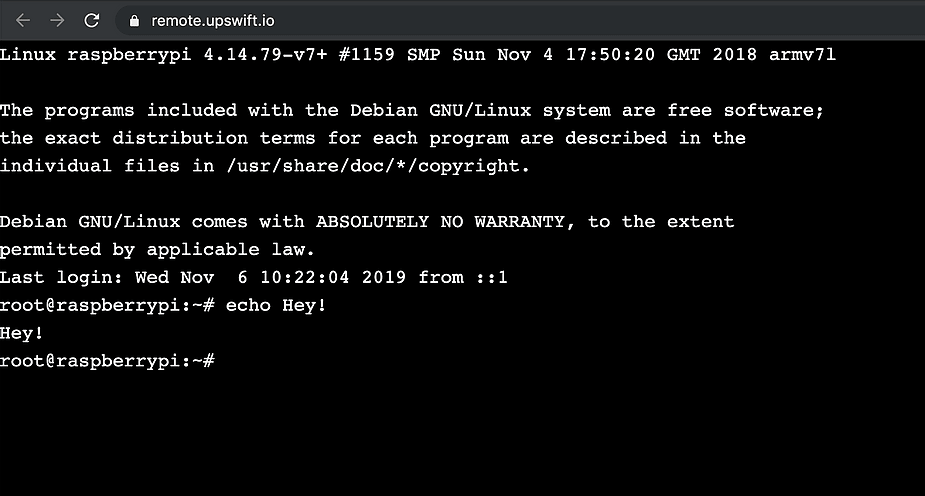
JFrog Connect provides a one-place to manage and maintain all edge devices remotely. The remote control tool is a ready-to-use JFrog Connect solution to access the device shell remotely.
The remote control provides a web shell interface that used for accessing and controlling the device without running any software on the controller side.